معماری و استراتژی امنیت سایبری
در سازمانهای بالغ، امنیت سایبری نه یک مجموعه ابزار، بلکه یک معماری تصمیمساز و کنترلگر در سطح کل سازمان است. در فضای پیچیده تهدیدات سایبری، رشد فناوری و الزامات حاکمیتی، عدم وجود یک معماری امنیتی یکپارچه منجر به افزایش ریسک، پیچیدگی، هزینههای غیرضروری و کاهش اثربخشی کنترلها خواهد شد.
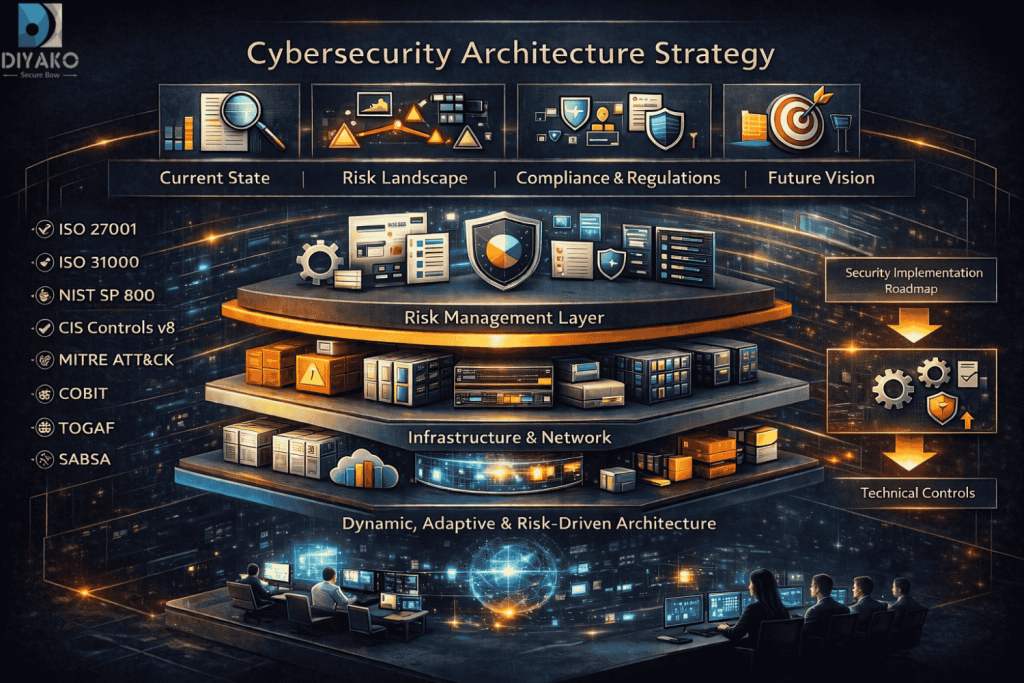
در کمان امن دیاکو (Diyako Secure Bow)، استراتژی معماری امنیت سایبری با رویکردی ریسکمحور، استانداردمحور و مستقل از فروشنده طراحی میشود تا امنیت بهصورت یکپارچه در تمامی لایههای سازمان نهادینه گردد.
این معماری بر اساس ترکیبی از عوامل زیر طراحی میشود:
و در نهایت، این معماری به یک نقشه راه مهندسیشده و قابل اجرا برای سازمان تبدیل میشود.
این رویکرد مبتنی بر استانداردها و فریمورکهای زیر است:
لایههای معماری امنیت شامل:
در این فاز، معماری امنیتی سازمان شما بهصورت مبتنی بر ریسک، مستقل از فروشنده و همراستا با اهداف کسبوکار طراحی میشود.
۱. جمعآوری اطلاعات (Data Gathering)
• شناسایی داراییهای حیاتی
• طبقهبندی دادهها
• تحلیل فرآیندهای کسبوکار
• بررسی ساختار فناوری اطلاعات
۲. تحلیل وضعیت موجود (As-Is Assessment)
• بررسی توپولوژی زیرساخت و شبکه
• ارزیابی کنترلهای امنیتی موجود
• تحلیل مستندات و معماری فعلی
۳. تحلیل چالشها و حوادث جاری
• بررسی رخدادهای امنیتی گذشته
• شناسایی نقاط ضعف عملیاتی
• تحلیل ریسکهای بالفعل و بالقوه
۴. تحلیل الزامات و نیازمندیها
• بررسی الزامات بالادستی
• استخراج نیازمندیهای دقیق کسبوکار
در این فاز، ریسکها بهصورت مهندسیشده تحلیل و به الزامات امنیتی قابل اجرا تبدیل میشوند.
۱. مدلسازی تهدید و سناریوهای حمله
• تحلیل تهدیدات
• تعریف سناریوهای حمله
۲. تحلیل آسیبپذیریها
• شناسایی نقاط ضعف در لایههای مختلف
۳. ارزیابی ریسک
• تحلیل احتمال و اثر
• اولویتبندی ریسکها
۴. استخراج الزامات امنیتی
• تبدیل ریسکها به کنترلهای مورد نیاز
در این فاز، معماری امنیتی هدف سازمان بهصورت یک نقشه مهندسیشده، قابل اجرا و مقیاسپذیر طراحی میشود.
• مبتنی بر ریسک و تهدیدات واقعی
• مستقل از فروشنده
• مقیاسپذیر و توسعهپذیر
• همراستا با اهداف کسبوکار
• قابل پایش و اندازهگیری
در این معماری، هر ریسک به کنترلهای مشخص نگاشت شده و هر کنترل در یکی از لایههای معماری پیادهسازی، پایش و ارزیابی میشود.
این معماری بهصورت پویا و قابل تکامل (Adaptive Architecture) طراحی میشود تا با رشد سازمان، تغییر تهدیدات و الزامات آینده همگام باشد.
در این فاز، مسیر پیادهسازی معماری بهصورت مرحلهبندیشده و قابل کنترل طراحی میشود.
• اولویتبندی پروژههای امنیتی
• تعیین وابستگیها و پیشنیازها
• زمانبندی اجرا
• برآورد منابع و هزینهها
در این فاز، اطمینان حاصل میشود که معماری طراحیشده بهصورت دقیق، استاندارد و بدون انحراف پیادهسازی گردد.
• استقرار نظارت در قالب ساختار حاکمیتی و PMO
• بازبینی طراحیهای تفصیلی
• نظارت بر پیادهسازی
• کنترل تنظیمات امنیتی
• جلوگیری از انحراف از معماری
• گزارش تحلیل وضعیت موجود
• گزارش ارزیابی ریسک
• طراحی معماری امنیت سایبری (سطح کلان و تفصیلی)
• نقشه راه اجرایی امنیت
• مستندات فنی و امنیتی
• لیست تجهیزات و راهکارها (LOM)
• اسناد RFP جهت مناقصه
• گزارشهای نظارت بر پیادهسازی


برای ارزیابی وضعیت فعلی و دریافت نقشهراه امنیتی اختصاصی، با کارشناسان مدیریت ارتباط با مشتریان (AM) کمان امن دیاکو در ارتباط باشید.
021-91691692 داخلی 1