طراحی امن (شبکه، زیرساخت، برنامههای کاربردی)
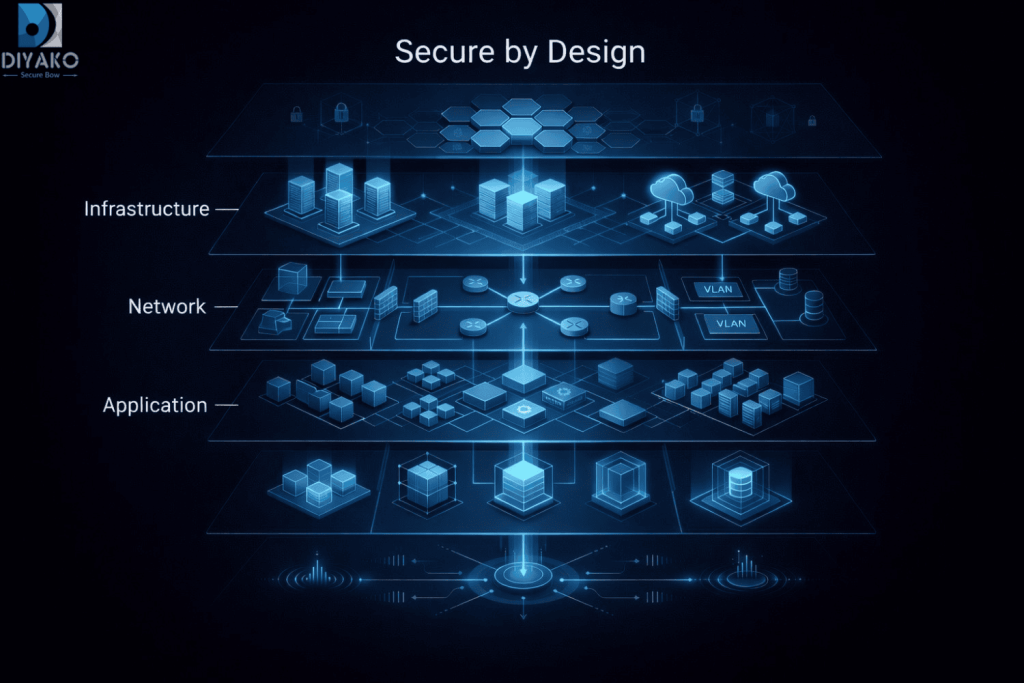
در دنیای امروز، امنیت سایبری نباید بهصورت مقطعی و ابزارمحور دیده شود؛ بلکه باید بهعنوان بخشی از طراحی بنیادین سازمان و همراستا با اهداف کسبوکار طراحی و مدیریت گردد. طراحی امن کمان امن دیاکو (Diyako Secure Bow) ستون فقرات امنیت سازمان شما است. امنیت یک ابزار یا لایه افزودنی نیست، بلکه بخشی از طراحی بنیادین سازمان (DNA) است. ما با رویکردی یکپارچه، امنیت را از طراحی تا اجرا و نظارت مدیریت میکنیم.
در این فاز، معماری امنیتی سازمان شما بهصورت مبتنی بر ریسک، مستقل از فروشنده و همراستا با اهداف کسبوکار طراحی میشود.
• امنیت زیرساخت (Infrastructure Security)
• امنیت شبکه (Network Security)
• امنیت اپلیکیشن و داده (Application & Data Security)
۱. جمعآوری اطلاعات و شناخت سازمان
• شناسایی داراییهای حیاتی (Critical Assets)
• طبقهبندی دادهها (Data Classification)
• درک نیازمندیهای کسبوکار و محدودیتها
۲. اعتبارسنجی و تحلیل وضعیت موجود
• بررسی مستندات، توپولوژیها و کنترلهای فعلی
• تحلیل شکافهای امنیتی (Gap Analysis)
۳. مصاحبه با ذینفعان
• استخراج دغدغهها، نیازها و ریسکهای پنهان
• همراستاسازی دیدگاه فنی و مدیریتی
۴. بازبینی پروژهها و معماریهای قبلی
• تحلیل سوابق اجرایی
• شناسایی ضعفهای تکرارشونده
۵. ارزیابی الزامات بالادستی و انطباق
• بررسی الزامات قانونی و حاکمیتی
• تطبیق با استانداردهایی مانند ISO 27001، NIST و CIS
۶. آیندهنگری و طراحی هدف (Future-State Design)
• تحلیل برنامههای توسعه سازمان
• طراحی معماری امن مقیاسپذیر و قابل توسعه
۷. ارزیابی ریسک امنیت سایبری
• شناسایی تهدیدات و سناریوهای حمله
• تحلیل احتمال و اثر
• اولویتبندی ریسکها
در این فاز، اطمینان حاصل میشود که فرآیند خرید تجهیزات و راهکارهای امنیتی،کاملاً همراستا با معماری طراحیشده، بهینه و بدون وابستگی به فروشنده انجام شود.
• تعریف الزامات فنی و امنیتی پیش از خرید
• ارزیابی تأمینکنندگان از منظر امنیت، کیفیت و انطباق
• بررسی و تأیید لیست تجهیزات و لایسنسها (LOM)
• کنترل جزئیات خرید شامل:
• ظرفیت (Sizing)
• لایسنسها
• سازگاری با زیرساخت موجود
• جلوگیری از Over/Under-Provisioning
• تضمین همراستایی کامل خرید با معماری امنیتی
در این فاز، دیاکو اطمینان میدهد که آنچه طراحی شده است، بدون انحراف، بهصورت دقیق و استاندارد پیادهسازی شود.
• بازبینی و تأیید طراحی تفصیلی (LLD)
• نظارت بر پیادهسازی تجهیزات توسط پیمانکار یا تیم داخلی مشتری
• بررسی و ارزیابی تنظیمات امنیتی (Secure Configuration Review)
• کنترل انطباق با استانداردها و بهروش های بین المللی
• شناسایی خطاهای پیادهسازی و ارائه اقدامات اصلاحی
• تأیید نهایی تحویل فنی (Technical Acceptance)
• گزارش جامع ریسک و آسیبپذیریها (Risk Register & Assessment)
• طراحی معماری امنیتی در سطح کلان و تفصیلی
• مستندات فنی و امنیتی قابل ارائه به مدیریت و تیمهای اجرایی
• لیست تجهیزات و لایسنسها (LOM)
• اسناد فنی جهت برگزاری مناقصه (RFP)
• گزارش نظارت بر اجرا و میزان انطباق با طراحی
در این فاز، GRC به یک سیستم پویا و قابل اندازهگیری تبدیل میشود که بهصورت مستمر وضعیت امنیت سازمان را ارزیابی و بهبود میدهد.
• تعریف شاخصهای کلیدی عملکرد (KPI) و شاخصهای ریسک (KRI)
• طراحی و استقرار داشبوردهای مدیریتی
• اتصال فرآیندهای GRC به مرکز عملیات امنیت
• تحلیل روندها و شناسایی نقاط ضعف
• اجرای چرخه بهبود مستمر امنیت
در این فاز، کلیه پروژههای مرتبط با امنیت و فناوری اطلاعات سازمان، از مرحله جمعآوری اطلاعات تا طراحی، پیادهسازی، امنسازی و ممیزی، در قالب یک ساختار حاکمیتی و تحت نظارت متمرکز مدیریت میشوند.
۱. استقرار مدل دفتر مدیریت پروژههای امنیت و فناوری در چارچوب حاکمیت سازمان
۲. نظارت بر چرخه کامل پروژهها:
• تحلیل و جمعآوری نیازمندیها
• طراحی معماری
• پیادهسازی و استقرار
• امنسازی و مقاومسازی
• ارزیابی و ممیزی امنیتی
۳. تضمین همراستایی تمامی پروژهها با:
• معماری امنیتی
• الزامات حاکمیت، ریسک و انطباق
• سیاستها و استانداردهای امنیتی سازمان
۴. ایجاد سازوکار نظارت و کنترل داخلی
۵. کنترل کیفیت، ریسک و انطباق در کل چرخه عمر پروژههای امنیتی و فناورانه
• چارچوب حاکمیت امنیت و مستندات سیاستها
• ماتریس نقشها و مسئولیتها
• گزارش ارزیابی ریسک و دفتر ثبت ریسک
• برنامه مدیریت و کاهش ریسک
• نگاشت ریسک به کنترلها
• گزارش تحلیل شکاف و نقشه راه انطباق
• مستندات کنترلها و شواهد اجرایی
• گزارشهای ممیزی و مدیریتی
• داشبوردهای مدیریتی و شاخصهای امنیتی
• مدل بلوغ حاکمیت، ریسک و انطباق
• گزارشهای نظارت بر پروژهها و میزان انطباق


برای ارزیابی وضعیت فعلی و دریافت نقشهراه امنیتی اختصاصی، با کارشناسان مدیریت ارتباط با مشتریان (AM) کمان امن دیاکو در ارتباط باشید.
021-91691692 داخلی 1